Before
moving on I would give you a special NOTICE In my Blog I have posted
everything I have written and If that post was not written by me than I
would write the source from where I have copied you can check it too.
So now lets move on to the Topic.
Facebook Hacking I
think most of you want to know how to hack Facebook password so in
this post I have posted everything you should know to hack someone’s
Facebook.
I will first introduce you with some Old style Hacking to Hardcore Hacking.
First one with the old and most the common method of getting someone’s password
i) Primary mail-
You register your Facebook account from primary mail like yahoo,
Gmail, etc. If you get access to someone’s primary mail than you can
goto Forgot your password link get the confirmation code and access the
account.
But How to get someone’s primary account’s password ?
Don’t
worry about it you should do just what I have told you firstly go to
yahoo.com(or other email provider) and press Forgot your password Link
there you will be asked some questions like Where were you born or
Where do you live By guessing this you can get the access to your
friends account.
ii) Social Engineering- I think many of you know what social engineering is. If you don’t know do not worry I am gonna explain it.
Social
Engineering is a process of manipulating someone by pretending that
they are some one(like IT officer) and need your information to do some
certain researches.
Here is an example of it :
Conversation between an Elite Hacker and a Newbie person(NooB)
Elite Hacker : Hi I got a good news for you
Newbie : What??
Elite Hacker : Do you want to learn hacking in few days.
Newbie now being excitedNewbie : Yeah Will you teach me ?
Elite Hacker : No I will post some of my Hacking Course video(top secret) in your account so give me your login details.
Newbie without thinking of anything gives his Facebook details.
This
is pretty much how someone can hack your Facebook by pretending. I
also used this process and hacked over 10+ account on my own.
iii) Friendship Attack-
This is not a hacking process but I have included you to give full
Guide. Ok friendship bomb is like Cheating your friend. You can install
some programs in your friends PC and you can threaten him/her to give
him/her password. Its kinna like Enemy attack.
iv) Garbage Dumping- There
are many people who use long password and to remember they note that
password in the paper and stick is somewhere usually behind the
Keyboard. Sometimes they accidentally throw that paper in
garbage. To check this some Professional Hacker (usually Crackers)
search in the garbage of the person’s house. Its not like WHO WILL DO
THIS KIND OF STUFF? but once you get the password or any sensible
information than you make get an employment in Garbage Factory :P.
v) Hiring a Hacker- There
is many hackers who crack someone’s password for you by paying. You
can even find someone online.(BUT NOT ME PLZ) and tell them to do.
Now
you have to be careful doing this cause there are many sites that tell
you that they will crack password for you by paying but all they are
doing is cheating on you so to confirm that they did hack the account
then tell them to give a screenshot of it or tell what message you have
send the user. This will make you safe if the hacker is fooling you.
vi) Spam Hack-
Now this is more interesting. You may sometime have got spammed by
some application in Facebook. Some application send message like Look
how this girl killed herself after seeing this {link} now when you
click on the link you will to be spammed some application spam by
sending message in chat and some in Wall post.
Now we are taking
this step to hack someone’s account. First create a application in
Facebook which spam the user by telling [you] hacked my account praise
him. Here you means your name like example If I have put Arpit there
than It will say Arpit Hacked my account praise him. Now after looking
this people or your friends will think that I have hacked him/her and
people will gather around you. A neat way to cheat people ;).
vii) JavaScript-
Now all of my favorite web programming language’s turn. If you think
JavaScript is useless than you are Wrong. Its an very powerful language.
Now
this trick doesn’t hack your friends password but make your friend
look like they hacked. You can get a complex JavaScript which will
display You got Owned Now by telling your friends to put that code in
the browser’s address bar and Press Enter they will see a Box with you
got owned It’s a good way to scare someone.
Now talking about some hardcore hacking \m/
i) Key logger- Very common and most used method for hacking someone’s Facebook account. You can download a key logger like Easy logger.
Download Easy logger by searching on Google. Now once you download Easy Logger See the image below.
Don’t put your Using Gmail account info in that cause if an hacker caught the keylogger than he can retrive your Password.
ii)Rats-
Now this is a real hardcore. Now this article is not written by me. To
save the time and delivery you fastly I have copied from The
Underground Hackers Handbook
Begin-
To show you an example of a malicious program, I will use a well known Windows Trojan, ProRat.
1.
Download ProRat. Once it is downloaded right click on the folder and
choose to extract it. A password prompt will come up. The password will
be “pro”.
2. Open up the program. You should see the following:
3. Next we will create the actual Trojan file. Click on Create and choose Create ProRat Server.
4.
Next put in your IP address so the server could connect to you. If you
don’t know your IP address click on the little arrow to have it filled
in for you automatically. Next put in your e-mail so that when and if a
victim gets infected it will send you a message. We will not be using
the rest of the options.
5. Click on the General Settings button
to continue. Here we will choose the server port the program will
connect through, the password you will be asked to enter when the victim
is infected and you wish to connect with them, and the victim name. As
you can see ProRat has the ability to disable the windows firewall and
hide itself from being displayed in the task manager.
6. Click on the Bind with File button
to continue. Here you will have the option to bind the trojan server
file with another file. Remember a trojan can only be executed if a
human runs it. So by binding it with a legitimate file like a text
document or a game, the chances of someone clicking it go up. Check the
bind option and select a file to bind it to. In the example I will use
an ordinary text document.
7. Click on the Server Extensions button
to continue. Here you choose what kind of server file to generate. I
will stick with the default because it has icon support, but exe’s looks
suspicious so it would be smart to change it.
8.
Click on Server Icon to continue. Here you will choose an icon for
your server file to have. The icons help mask what the file actually
is. For my example I will choose the regular text document icon since
my file is a text document.
9. Finally click on Create Server to, you guessed it, create the server file.
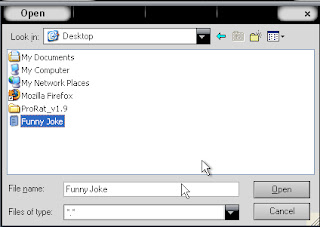
10.
A hacker would probably rename it to something like “Funny Joke” and
send it as an attachment to some people. A hacker could also put it up
as a torrent pretending it is something else, like the latest game that
just came out so he could get people to download it.
11. Now, I will show you what happens when a victim installs the server onto his computer and what the hacker could do next.
12.
I’m going to run the server on my own computer to show you what would
happen. Once I run it the trojan will be installed onto my computer in
the background. The hacker would then get a message telling him that I
was infected. He would then connect to my computer by typing in my IP
address, port and clicking Connect. He will be asked for the password
that he made when he created the server. Once he types it in, he will
be connected to my computer and have full control over it.
15. Below is an image of my task bar after the hacker clicks on Hide Start Button.
16. Below is an image of what the hacker would see if he chose to take a screen shot of the victims screen.
As
you saw in the above example, a hacker can do a lot of silly things or
a lot of damage to the victim. ProRat is a very well known trojan so
if the victim has an anti-virus program installed he most likely won’t
get infected. Many skilled hackers can program their own viruses and
Trojans that can easily bypass anti-virus programs.
iii) Phishing- Now you can get info about Phishing any where in Google Search in Google and Learn it.
SECURITY OWNED IS NOT THE AUTHOR OF THIS POST
THIS POST IS CREATE BY
http://www.devilscafe.in
AUTHOR:MINHAL MENDHI
THIS POST IS COPYRIGHT PROTECTED
BY DEVILSCAFE
FIND SME COOL TRICK FROMhttp://www.devilscafe.in